This powerful Iranian product is an integrated system for security information and event management (SIEM), which collecting logs from various sensors and correlates all events using various scenarios.
This system collects network nodes information, checks their vulnerabilities and reports security holes. Momentarily, Picket receives thousands of data and events from computers, servers, network devices, software and compares the data behavior with cyberattack patterns and produces different security alerts and reports.
It should be noted that this system runs parallel and adjacent to the main network and doesn’t effects on normal operations. In fact, it only checks attackers, malware and network traffic behavior patterns without interfering with content of information packets, and assesses the status of network in real-time based on security scenarios, providing appropriate responds if necessary.
Some Features of Main Components of the System
User Interface
The system UI is user-friendly and designed in a way that menus and other visual features are available based on their importance and application. This UI is completely web-based and provides remote access with security standards.
Reporting and Dashboard
Different predefined reports, standard outputs and also scheduled reporting capabilities meet all security and management needs. At the same time, it is possible to create various and new reports for the user. The charts are completely intelligible and understandable and provide the highest amount of useful insight in the shortest time.
Intelligence and Correlation Processing
The correlation engine of the system uses a variety of multi-dimensional correlation algorithms and with minimum false positives, prioritizes events based on their importance, occupying less system resources by processing more important events. Considering the importance of assets, priority and importance of events, evaluates risks on the go and detects them at early stages.
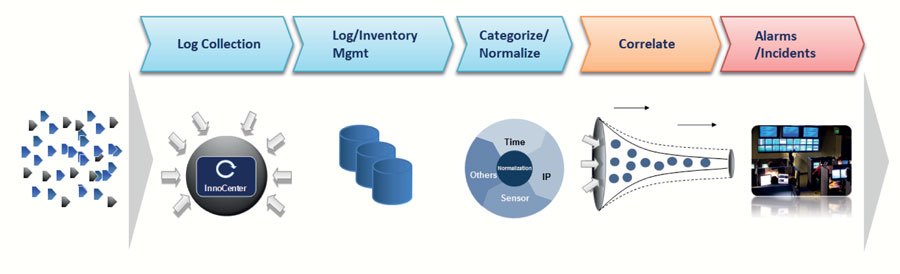
Data Collection
The system has sensors that collect events information from all network components without affecting its normal performance. It has no limits in receiving data from new equipment and other network components. This layer includes several sensors to analyze network traffic and also different Intrusion Detection Sensors (IDSs) such as reactive, passive, network-based, host-based, anomaly-based, and signature-based sensors.
Other Features
- No limitation in number of policies, with the ability to add security scenarios by user
- Comprehensive knowledge database
- Supporting unlimited users and user groups with advanced user management
- Sending email and SMS upon alert including ticketing system
- Interoperability with other security operations centers
- Vulnerability scanning, providing an accurate solution to mitigate them
- Processing vulnerability scanning results in correlation process engine
- Complete monitoring of inbound and outbound network traffic based on each component along with visual representation
- Online and offline update is available
Tags: Sciences Green Inc ، علوم سبز ، SGI ، اینترنت اشیا ، Internet of Things ، IoT ، شهر هوشمند ، smart city ، امنیت سایبری ، Cyber security ، مخابرات ، Telecommunication ، پیکت ، SOC ، پردازش یکپارچه ، کاهش تهدیدات ، مدیریت رخدادها و اطلاعات امنیتی ، SIEM ، آسیبپذیری ، جمعآوری دادهها ، گزارشدهی ، پردازش همبستگی ، Intelligence and Correlation Processing، Integrated processing and threat mitigation ، comprehensive centralized solution for network performance monitoring